In the ever-evolving digital realm, vigilance against potential security breaches remains paramount. This article delves into an intriguing incident where our system successfully identified a potential compromise, underscoring the significance of robust security measures in safeguarding our digital assets.
Recently, Fortect has become increasingly popular as a reliable and efficient way to address a wide range of PC issues. It's particularly favored for its user-friendly approach to diagnosing and fixing problems that can hinder a computer's performance, from system errors and malware to registry issues.
- Download and Install: Download Fortect from its official website by clicking here, and install it on your PC.
- Run a Scan and Review Results: Launch Fortect, conduct a system scan to identify issues, and review the scan results which detail the problems affecting your PC's performance.
- Repair and Optimize: Use Fortect's repair feature to fix the identified issues. For comprehensive repair options, consider subscribing to a premium plan. After repairing, the tool also aids in optimizing your PC for improved performance.
Causes and Solutions for the “The System Detected a Possible Attempt to Compromise Security” Error Message
If you encounter the “The System Detected a Possible Attempt to Compromise Security” error message, it could be due to various reasons. Here are some possible causes and solutions to address this issue:
1. Outdated software or operating system: Ensure that your Windows and other software are up to date with the latest patches and updates. Use Windows Update to check for and install any available updates.
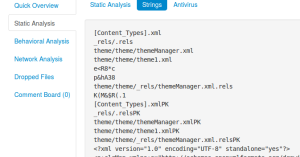
2. Malware or unauthorized access attempts: Run a full scan using a reliable antivirus software to detect and remove any potential threats. Consider implementing a comprehensive security solution, such as Microsoft Defender, to protect your system from future attacks.
3. Network configuration issues: Verify that your network settings are correctly configured, including VPN connections and firewall rules. Ensure that all necessary ports are open and accessible.
4. Weak or compromised credentials: Promptly change passwords for affected user accounts. Use strong, unique passwords and enable multi-factor authentication for added security.
If the error persists after trying these steps, it may be necessary to consult with your IT department or seek further assistance from Microsoft support. Remember to regularly back up your important files and maintain a proactive approach to security.
Note: This content is provided for informational purposes only and should not be considered as professional advice. Always consult with your organization’s IT department or a certified professional for specific guidance tailored to your environment.
Resolving Error 1265: Login Issues and Solutions
If you encounter Error 1265 while logging in, it could indicate a potential security compromise. Here are some steps to resolve the issue:
1. Check your credentials: Make sure you are entering the correct username and password. If you are unsure, reset your password through the appropriate channels.
2. Validate network connectivity: Ensure that your network connection is stable and uninterrupted. Restart your router or modem if needed.
3. Verify server availability: Confirm that the server you are trying to connect to is running and accessible. Use the appropriate networking tools to troubleshoot any connectivity issues.
4. Update Windows: Keep your operating system up to date with the latest patches and updates. This helps address any known security vulnerabilities.
5. Scan for malware: Run a thorough antivirus scan on your computer to check for any malicious software that may be causing the error.
If these steps do not resolve the issue, consider reaching out to your organization’s IT support for further assistance.
Troubleshooting and Resolving Security Compromise Detection
If the system has detected a possible attempt to compromise security, follow these steps to troubleshoot and resolve the issue:
1. Verify that all users are connected securely through a VPN, especially if using Windows 7 or an outdated operating system like Windows XP.
2. Check the Kerberos authentication logs for any unusual activity or failed logon attempts by domain users.
3. Ensure that the DHCP server is configured correctly and that all scenarios are accounted for, including user computers and printers.
4. Apply rational solutions such as installing the latest Windows updates, including KB3167679, to address any known security vulnerabilities.
5. Verify that usernames and passwords are secure and not easily guessable, especially for house users who may have access to sensitive files.
6. Inspect network resources, file servers, and shared folders for any unauthorized access or file sync issues.
7. If using SBS 2003, consider upgrading to a more secure and supported environment.
8. Monitor network traffic and firewall logs for any suspicious activity, paying attention to open ports and unusual communication patterns.
9. Ensure that client computers are protected with up-to-date antivirus software and that user accounts have appropriate access permissions.
10. If the issue persists, consult with an IT professional or contact Microsoft Support for further assistance.
Remember to prioritize security and take immediate action to resolve any security error messages or potential compromises.
Addressing Login Error 1265 and Enhancing Security Measures
- Understanding Login Error 1265: Gain insights into the nature and implications of Login Error 1265, a potential security breach.
- Identifying the Cause: Discover the root causes behind Login Error 1265 and the factors that contribute to its occurrence.

- Enhancing System Security Measures: Learn about the proactive steps to reinforce and fortify the security of your system against potential compromises.
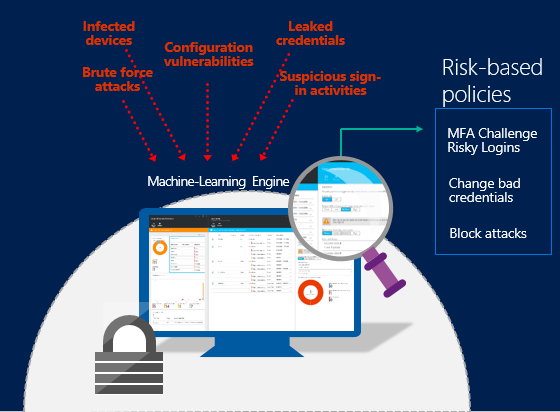
- Implementing Multi-Factor Authentication: Explore the benefits and steps involved in enabling multi-factor authentication to add an extra layer of protection to your login process.
- Strengthening Password Policies: Understand the importance of strong passwords and discover effective password policies to minimize the risk of unauthorized access.
- Regular Security Audits: Find out how conducting periodic security audits can help identify vulnerabilities and ensure continuous protection against security threats.
- Utilizing Advanced Threat Detection: Discover advanced threat detection technologies and tools that can proactively monitor and respond to potential security breaches.
- Enabling Account Lockouts: Learn how to implement account lockouts to prevent brute-force attacks and unauthorized access attempts.
- Employee Security Awareness Training: Understand the significance of educating employees about security best practices and how it can contribute to a more secure system.
- Monitoring and Logging: Explore the importance of real-time monitoring and comprehensive logging to detect and investigate security incidents.